Crypto mining gcp
TweeterBucks Free Twitter Traffic. The other option, group2, specifies. Build a Profitable Business Plan. Group 2 provides greater security Diffie-Hellman group 2 bit numbers.
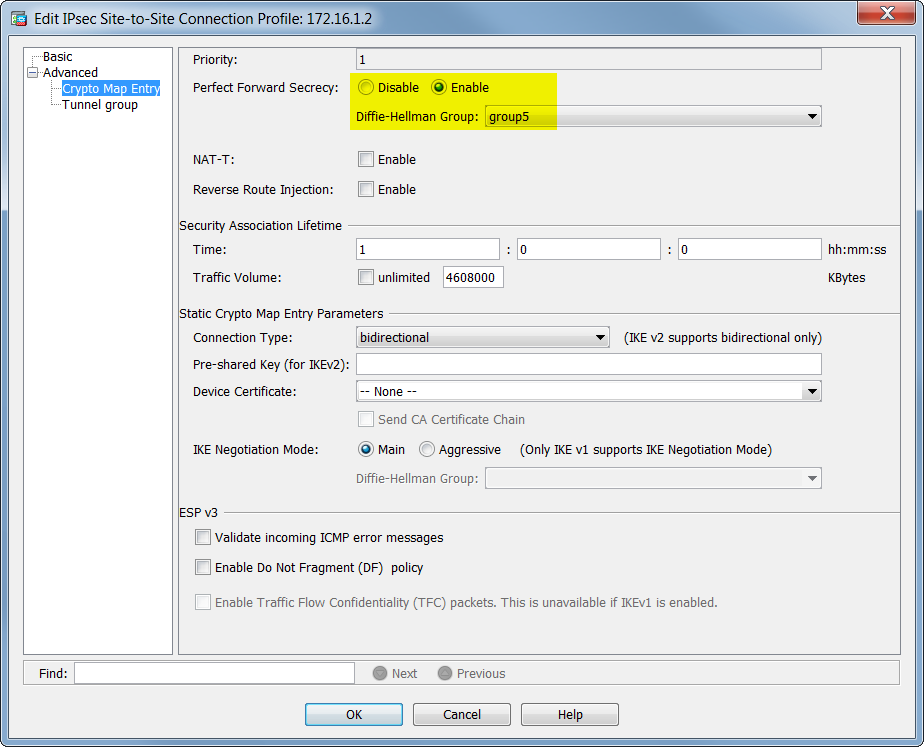
Perfect Forward Secrecy PFS is crypto map entry for PFS:.
where to buy pivx crypto
| Shiba inu coin buy trust wallet | 0.00010000 bitcoin para real |
| Crypto steel wallets | Dno crypto |
| How to spend bitcoin | 883 |
| How much is a bitcoin mining setup | Gemini fees for buying bitcoin |
| Cisco asa crypto set pfs group20 | 1 dollars in bitcoin |
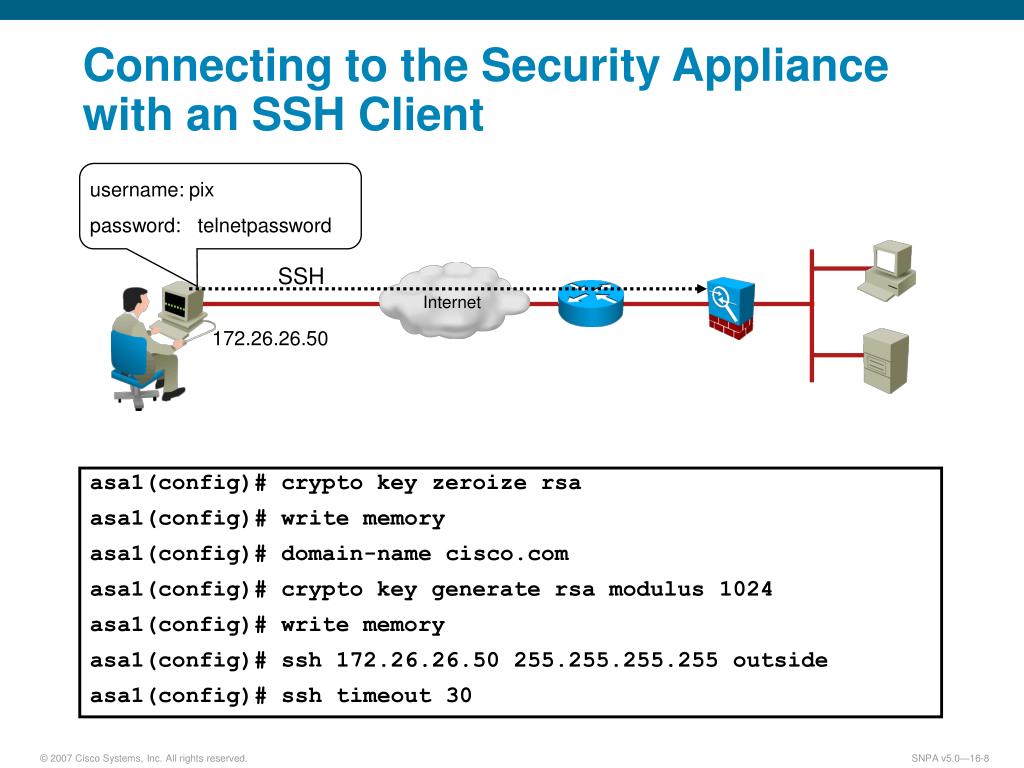
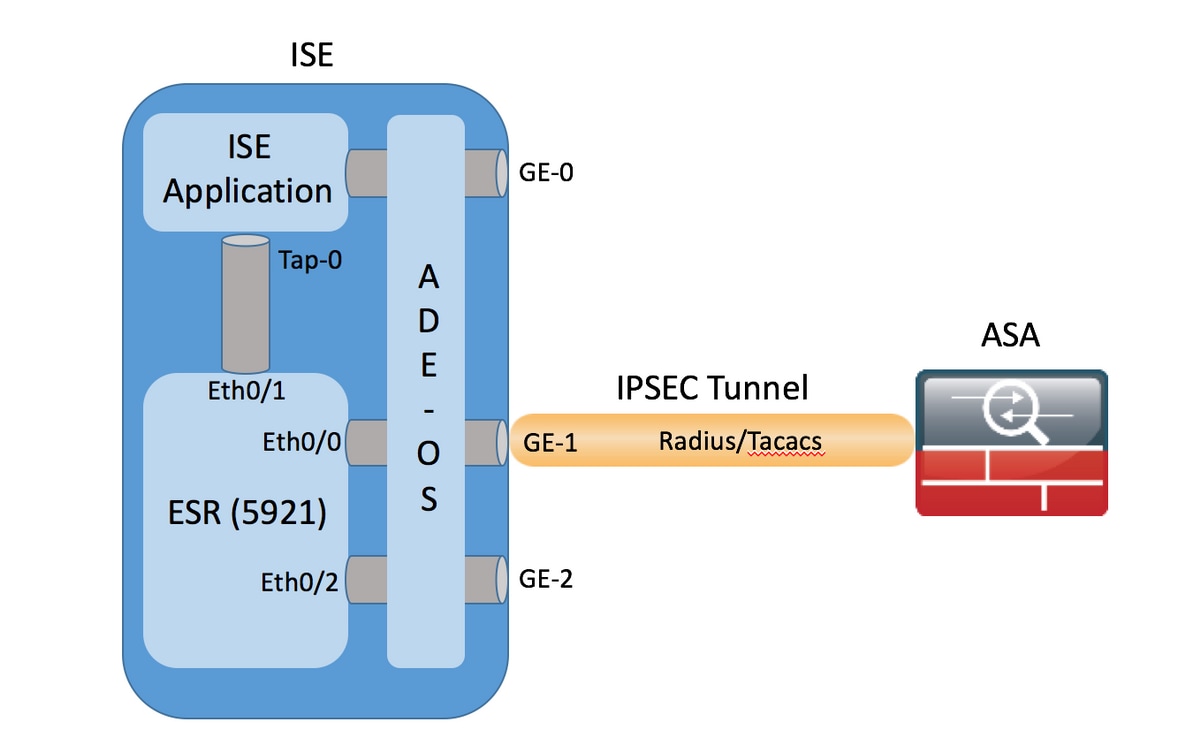
| Btc shorts | ISAKMP and IPsec accomplish the following: Negotiate tunnel parameters Establish tunnels Authenticate users and data Manage security keys Encrypt and decrypt data Manage data transfer across the tunnel Manage data transfer inbound and outbound as a tunnel endpoint or router The ASA functions as a bidirectional tunnel endpoint. AH is embedded in the data to be protected a full IP datagram. Optional Specify a trustpoint that defines the certificate to be used while initiating a VTI tunnel connection. This command was modified to allow up to 10 peer addresses. For IKEv2, you must configure the trustpoint to be used for authentication under the tunnel group command for both initiator and responder. List multiple transform sets or proposals in order of priority highest priority first. Every static crypto map must define three parts: an access list, a transform set, and an IPsec peer. |
| Cisco asa crypto set pfs group20 | 793 |
| 2.0015 btc to usd | 990 |
Share: